Why we built Launchpad
We are building Launchpad to help democratize the most powerful technology humans ever built. Read why we are joining the fight against closed-source AI.
Solana MEV-Validator Server Program: Jito & Latitude.sh Partnership
Unlock the full potential of MEV on Solana with a powerful validator at a discounted price. Sign up for the Latitude.sh server program today.
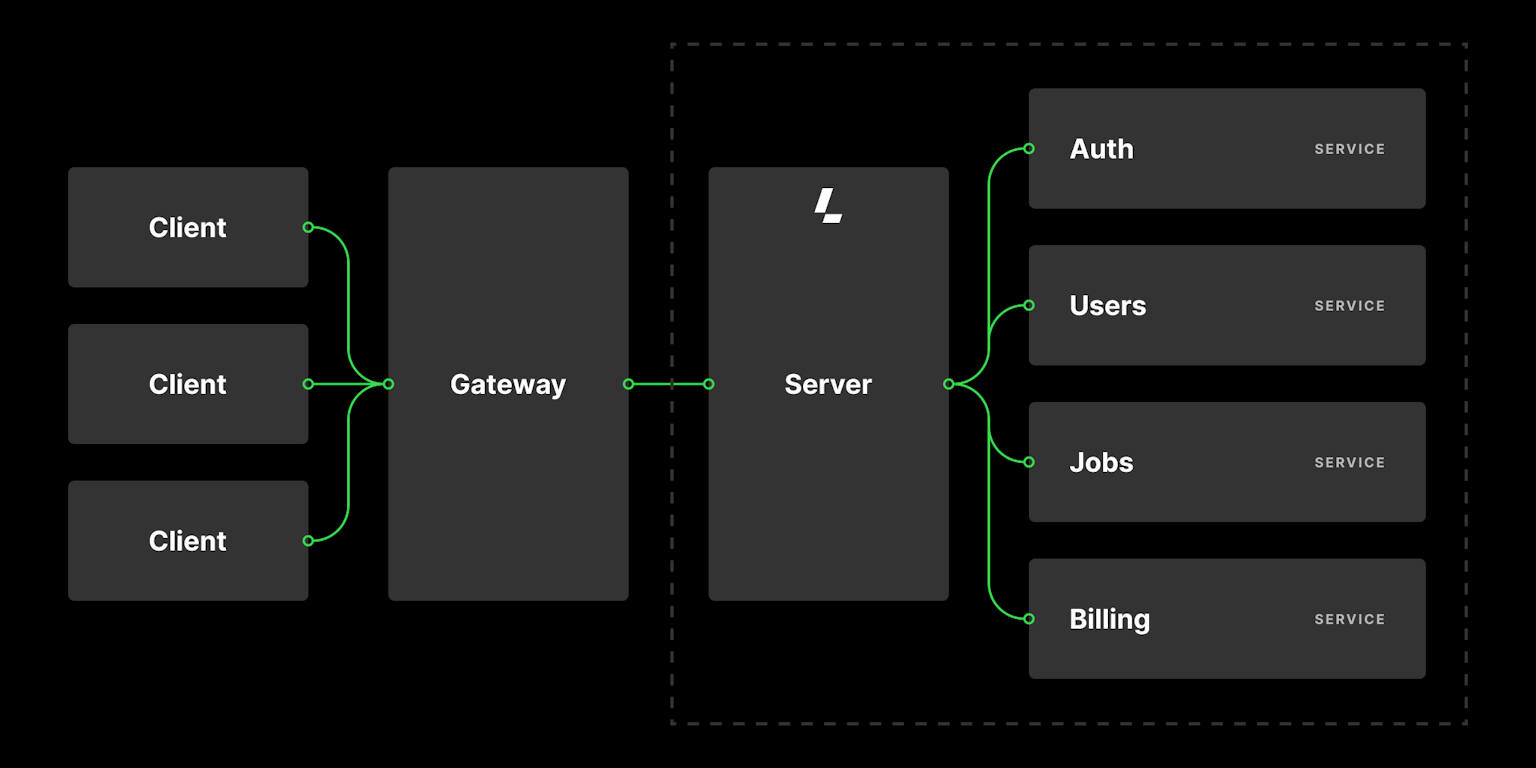
Building a microservice application from Day 1
A Latitude.sh customer ran an experiment to find the best cloud provider for deploying scalable microservice applications.
Maxihost is now Latitude.sh
Today, we have some very exciting news about the evolution of our company. Maxihost is now Latitude.sh.
Latitude.sh Brings its Powerful Bare Metal Cloud Platform to London
Latitude.sh's new location in London will support cloud infrastructure requirements for Gaming, Streaming and Web3 applications in the UK and neighboring European countries.
Ankr Partners with Bare Metal Cloud Provider Latitude.sh to Scale Web3 Infrastructure Globally
Latitude.sh will be delivering more than 100 bare metal servers to Ankr across 13 global Edge locations.
Latitude.sh Selects Scala Data Centers to Extend Brazil Data Center Footprint
Latitude.sh's new MH2 facility will be deployed at Scala's SP2 data center in São Paulo, enabling Latitude.sh's global bare metal offering from Scala's ecosystem
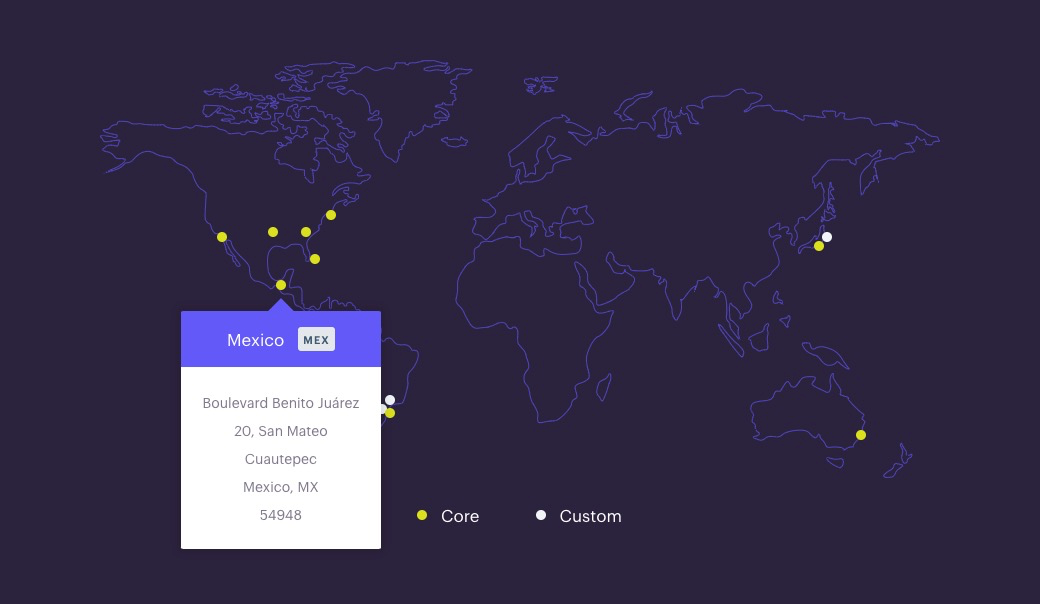
Expanding Latitude.sh's footprint to Mexico
We are excited to announce the expansion of our global presence with a new platform region in Mexico City. This adds a third location to our Latin America footprint, following our established locations in Brazil and Chile.
Latitude.sh Expands Footprint to Mexico City via KIO Networks
Latitude.sh Brings Powerful, Automated Bare Metal Servers for Cloud and Edge Applications to Critical Latin America Interconnection Hub
Deploy your apps on Metal with Cloud 66
Latitude.sh partnered with Cloud 66 to make deploying your apps on the Edge more straightforward. With Latitude.sh and Cloud66, developers can deploy their applications on bare metal servers by simply pushing to master.